Here is a screenshot of the message spreading:

The real URL is being displayed in the status bar.
I personaly used DynDNS some time ago... anyway.
This malware did trigger an alert from:
- Kaspersky
- IE 9 Smart screen filter
But the thing is, Kaspersky was talking about an EXE packer/wrapper. That drew my attention.
So, here we are, let's have a look at the file:
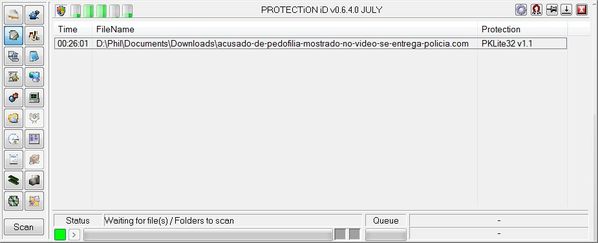
So, yeah, the file is being protected by PKLite32 v1.1!
That's what KAV was saying, allright. But, to me, it is not because a file is being protected or obfuscated by a specific technology, that this file is a malware for sure...
More details to come, I'm investigating that in deep...
BTW, here are the full VT's results
(see https://www.virustotal.com/file-scan/report.html?id=48a93a6d8384c58d07285826a00ff3e8c553676903e59e1273316b32c4dc9af3-1311421202# ):
| Antivirus | Version | Last update | Result |
|---|---|---|---|
| AhnLab-V3 | 2011.07.23.00 | 2011.07.22 | Packed/Win32.Morphine |
| AntiVir | 7.11.12.64 | 2011.07.22 | TR/Spy.Banker.253440.3 |
| Antiy-AVL | 2.0.3.7 | 2011.07.23 | - |
| Avast | 4.8.1351.0 | 2011.07.23 | Win32:Rootkit-gen [Rtk] |
| Avast5 | 5.0.677.0 | 2011.07.23 | Win32:Rootkit-gen [Rtk] |
| AVG | 10.0.0.1190 | 2011.07.23 | PSW.Banker6.AFP |
| BitDefender | 7.2 | 2011.07.23 | Trojan.Generic.6346484 |
| CAT-QuickHeal | 11.00 | 2011.07.23 | - |
| ClamAV | 0.97.0.0 | 2011.07.23 | - |
| Commtouch | 5.3.2.6 | 2011.07.23 | W32/Infostealer.A!Maximus |
| Comodo | 9476 | 2011.07.23 | TrojWare.Win32.TrojanDownloader.Dadobra.~JN12 |
| DrWeb | 5.0.2.03300 | 2011.07.23 | Trojan.DownLoader4.18737 |
| Emsisoft | 5.1.0.8 | 2011.07.23 | Gen.Trojan.TaskDisabler!IK |
| eSafe | 7.0.17.0 | 2011.07.21 | - |
| eTrust-Vet | 36.1.8459 | 2011.07.22 | - |
| F-Prot | 4.6.2.117 | 2011.07.22 | W32/Infostealer.A!Maximus |
| F-Secure | 9.0.16440.0 | 2011.07.23 | Trojan.Generic.6346484 |
| Fortinet | 4.2.257.0 | 2011.07.23 | - |
| GData | 22 | 2011.07.23 | Trojan.Generic.6346484 |
| Ikarus | T3.1.1.104.0 | 2011.07.23 | Gen.Trojan.TaskDisabler |
| Jiangmin | 13.0.900 | 2011.07.22 | Trojan/Hosts2.bd |
| K7AntiVirus | 9.108.4937 | 2011.07.22 | Trojan |
| Kaspersky | 9.0.0.837 | 2011.07.23 | Trojan.Win32.Hosts2.gen |
| McAfee | 5.400.0.1158 | 2011.07.23 | Generic.dx!babe |
| McAfee-GW-Edition | 2010.1D | 2011.07.23 | Generic.dx!babe |
| Microsoft | 1.7104 | 2011.07.23 | Trojan:Win32/Comrerop |
| NOD32 | 6317 | 2011.07.23 | Win32/Qhost.Banker.JE |
| Norman | 6.07.10 | 2011.07.22 | W32/Suspicious_Gen2.NQJPD |
| nProtect | 2011-07-23.01 | 2011.07.23 | Generic.Banker.Delf.1F2FDCDB |
| Panda | 10.0.3.5 | 2011.07.22 | - |
| PCTools | 8.0.0.5 | 2011.07.23 | Spyware.Keylogger!rem |
| Prevx | 3.0 | 2011.07.23 | - |
| Rising | 23.67.04.03 | 2011.07.22 | - |
| Sophos | 4.67.0 | 2011.07.23 | Mal/Behav-180 |
| SUPERAntiSpyware | 4.40.0.1006 | 2011.07.23 | - |
| Symantec | 20111.1.0.186 | 2011.07.23 | Spyware.Keylogger |
| TheHacker | 6.7.0.1.260 | 2011.07.22 | - |
| TrendMicro | 9.200.0.1012 | 2011.07.23 | TROJ_COMREROP.AA |
| TrendMicro-HouseCall | 9.200.0.1012 | 2011.07.23 | TROJ_COMREROP.AA |
| VBA32 | 3.12.16.4 | 2011.07.22 | suspected of Unknown.Win32Virus |
| VIPRE | 9939 | 2011.07.23 | Trojan.Win32.Generic!BT |
| ViRobot | 2011.7.23.4585 | 2011.07.23 | - |
| VirusBuster | 14.0.134.1 | 2011.07.22 | - |
| MD5: bcd76d2daa826d9737e2d63025ed03fc |
| SHA1: 8925af7ea3dba240087049ee3a2017b734d98264 |
| SHA256: 48a93a6d8384c58d07285826a00ff3e8c553676903e59e1273316b32c4dc9af3 |
| File size: 253440 bytes |
| Scan date: 2011-07-23 11:40:02 (UTC) |
As we can see, generic/heuristic/genotype signature technologies tend to prove their efficiency.
ThreatExpert does confirm Kaspersky detects PkLite32 compression: http://www.threatexpert.com/report.aspx?md5=bcd76d2daa826d9737e2d63025ed03fc
More to come...


