18 mars 2010
4
18
/03
/mars
/2010
21:11
This is not the first, but I find this case quite interesting.
Some PC that were formerly compromised (I don't know the malware details at the time of writing) started around 6PM UTC to send messages to their MSN contacts.
Here is a sample of the message:

Here is the suspicious web link : www.facebook- id.us/profil.php?=PICT18082010
Obviously, DON'T CLICK ON THAT!
Please note the exact syntax of the word 'facebook' in the URL! Who's gonna notice the '-us' at the end?
On a safe and hardened operating system (such as a BSD derivative...), I see that the browser will directly try to download an exefile, which name is: PICT18082010-jpg-www-facebook-com.scr
Be carefull since this file has got a fake icon: it looks like a picture (some kindda JPG file I'd say).
Some people had already tried VT for this sample:
http://forum.malekal.com/www-facebook-profil-php-pict18082010-t24041.html
The AV protection coverage does not look that good:
http://www.virustotal.com/analisis/72c7b58796d12793cf39debb98344bb71ac79670828f8db8540b343eedd5c83c-1268935265
14% !!
So now, let's try to see who's behind that domain facebook-id.us.
The first WhoIs results look stange:
http://www.domaincrawler.com/domains/view/facebook-id.us
Wow... it looks like Yahoo has got a problem... is it being as a real component of the attack campaign?
Ripe.net did not give me any information. But another WhoIs tool seemed to have more detailed information:
http://www.raynette.fr/services/whois/index.php?action=domain_info&domain=facebook-id.us
Still a reference to Yahoo: YNS1.YAHOO.COM
Quite worying if Yahoo has indeed been compromised.
Here is what the SFR DNS say about it:
And OpenDNS:
Okay those different DNS seem to be consistent. Let's check now the NS that is said to be authoritative on the domain.
Hardly kidding but the IP address pointed by yns1.yahoo.com seems to be quite anonymous: http://www.db.ripe.net/whois?form_type=simple&full_query_string=&searchtext=98.136.43.32&submit.x=12&submit.y=7&submit=Search
At this moment, I really wonder shat's happening. Yahoo NS does not reply to a standard query for "yahoo.com", but it does respond to a query for "facebook-id.us"!!
What about URL filtering ?
- Trustedsource (McAfee): not listed [reported]
- SurfControl: not listed [reported]
- NetCraft: high risk, but no real warning [reported]
- Firefox/Chrome (Google SafeBrowsing): no warning. [reported]
If you acces the website using Firefox (and Firebug ;), you may obtain a few more details:
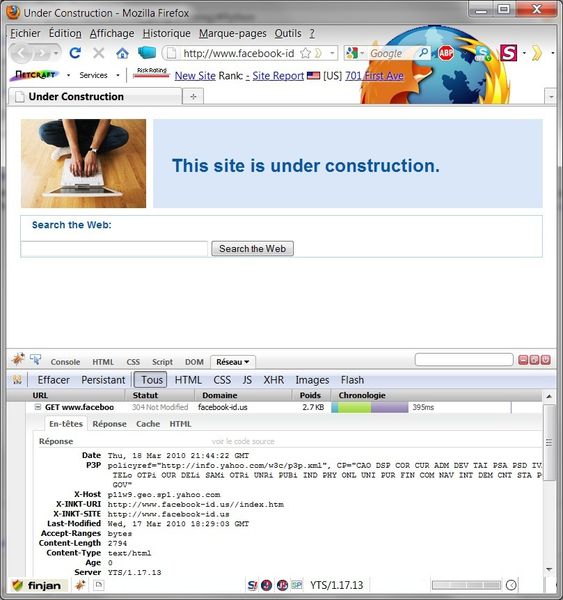
Please note the 'YTS' server and the host: p11w9.geo.sp1.yahoo.com!!
FYI 'YTS' apparently stands for Yahoo! Trafic Server... see http://acronyms.thefreedictionary.com/Yahoo!+Traffic+Server
Then now, let's try to figure what's going on the Yahoo.com NS. I'm gonna use a Yahoo NS server as one of my DNS (nslookup tool). Let's say ns1.yahoo.com.
Here are the results:
> server ns1.yahoo.com
Please not that the yns1.yahoo.com does not generate a 'non authoritative answer' within the reply of the official Yahoo DNS. So, we can honestly suppose the A pointer (for yns1.yahoo.com) has been added to the DNS, and... well... they've been rooted.
Therefore, until I've proof of the contrary, I do believe Yahoo NS (and probably one server) have been compromised. And Yahoo is taking part of an attack over MSN...
More to come if I can.
Some PC that were formerly compromised (I don't know the malware details at the time of writing) started around 6PM UTC to send messages to their MSN contacts.
Here is a sample of the message:

Here is the suspicious web link : www.facebook- id.us/profil.php?=PICT18082010
Obviously, DON'T CLICK ON THAT!
Please note the exact syntax of the word 'facebook' in the URL! Who's gonna notice the '-us' at the end?
On a safe and hardened operating system (such as a BSD derivative...), I see that the browser will directly try to download an exefile, which name is: PICT18082010-jpg-www-facebook-com.scr
Be carefull since this file has got a fake icon: it looks like a picture (some kindda JPG file I'd say).
Some people had already tried VT for this sample:
http://forum.malekal.com/www-facebook-profil-php-pict18082010-t24041.html
The AV protection coverage does not look that good:
http://www.virustotal.com/analisis/72c7b58796d12793cf39debb98344bb71ac79670828f8db8540b343eedd5c83c-1268935265
14% !!
So now, let's try to see who's behind that domain facebook-id.us.
The first WhoIs results look stange:
http://www.domaincrawler.com/domains/view/facebook-id.us
Wow... it looks like Yahoo has got a problem... is it being as a real component of the attack campaign?
Ripe.net did not give me any information. But another WhoIs tool seemed to have more detailed information:
http://www.raynette.fr/services/whois/index.php?action=domain_info&domain=facebook-id.us
Still a reference to Yahoo: YNS1.YAHOO.COM
Quite worying if Yahoo has indeed been compromised.
Here is what the SFR DNS say about it:
Nom : sbs-p11p.asbs.yahoodns.net
Addresses: 69.147.83.187
98.136.50.138
69.147.83.188
Aliases: www.facebook-id.us
p11-pprr.geo.premiumservices.yahoo.com
And OpenDNS:
> www.facebook-id.us
Serveur : resolver1.opendns.com
Address: 208.67.222.222
Réponse ne faisant pas autorité :
Nom : sbs-p11p.asbs.yahoodns.net
Addresses: 98.136.50.138
69.147.83.188
69.147.83.187
Aliases: www.facebook-id.us
p11-pprr.geo.premiumservices.yahoo.com
Okay those different DNS seem to be consistent. Let's check now the NS that is said to be authoritative on the domain.
> server yns1.yahoo.com
Serveur par defaut : yns1.yahoo.com
Address: 98.136.43.32
> yahoo.com Serveur : yns1.yahoo.com
Address: 98.136.43.32
*** Query refused
> facebook-id.us
Serveur : yns1.yahoo.com
Address: 98.136.43.32
Nom : facebook-id.us
Addresses: 69.147.83.188
69.147.83.187
98.136.50.138
Hardly kidding but the IP address pointed by yns1.yahoo.com seems to be quite anonymous: http://www.db.ripe.net/whois?form_type=simple&full_query_string=&searchtext=98.136.43.32&submit.x=12&submit.y=7&submit=Search
At this moment, I really wonder shat's happening. Yahoo NS does not reply to a standard query for "yahoo.com", but it does respond to a query for "facebook-id.us"!!
What about URL filtering ?
- Trustedsource (McAfee): not listed [reported]
- SurfControl: not listed [reported]
- NetCraft: high risk, but no real warning [reported]
- Firefox/Chrome (Google SafeBrowsing): no warning. [reported]
If you acces the website using Firefox (and Firebug ;), you may obtain a few more details:
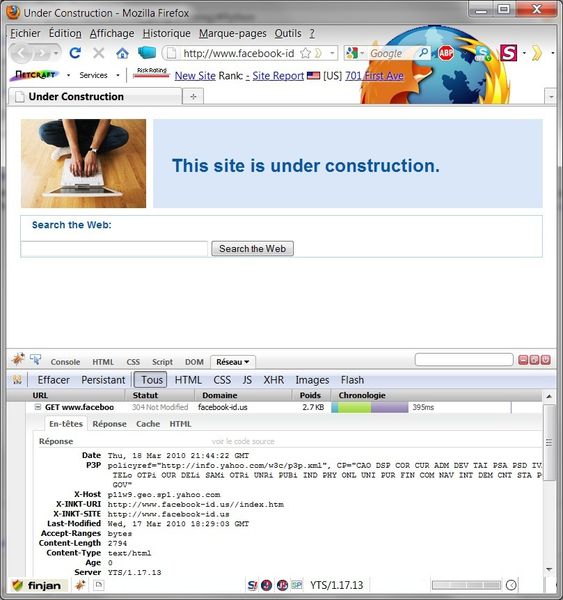
Please note the 'YTS' server and the host: p11w9.geo.sp1.yahoo.com!!
FYI 'YTS' apparently stands for Yahoo! Trafic Server... see http://acronyms.thefreedictionary.com/Yahoo!+Traffic+Server
Then now, let's try to figure what's going on the Yahoo.com NS. I'm gonna use a Yahoo NS server as one of my DNS (nslookup tool). Let's say ns1.yahoo.com.
Here are the results:
> server ns1.yahoo.com
Serveur par defaut : ns1.yahoo.com
Address: 68.180.131.16
> yahoo.com
Serveur : ns1.yahoo.com
Address: 68.180.131.16
Nom : yahoo.com
Addresses: 67.195.160.76
69.147.114.224
69.147.125.65
72.30.2.43
98.137.149.56
209.131.36.159
209.191.93.53
209.191.122.70
> yns1.yahoo.com
Serveur : ns1.yahoo.com
Address: 68.180.131.16
Nom : yns1.yahoo.com
Address: 98.136.43.32Please not that the yns1.yahoo.com does not generate a 'non authoritative answer' within the reply of the official Yahoo DNS. So, we can honestly suppose the A pointer (for yns1.yahoo.com) has been added to the DNS, and... well... they've been rooted.
Therefore, until I've proof of the contrary, I do believe Yahoo NS (and probably one server) have been compromised. And Yahoo is taking part of an attack over MSN...
More to come if I can.


